Notizie per Categorie
Articoli Recenti
- [In preview] Public Preview: Azure Front Door Premium now supports Azure Private Link origins in UAE North 10 Febbraio 2026
- [In preview] Public Preview: Azure Front Door Premium now supports Azure Private Link origins in UAE North 10 Febbraio 2026
- [Launched] Generally Available: Azure Databricks Supervisor Agent 10 Febbraio 2026
- [Launched] Generally Available: Azure Databricks Supervisor Agent 10 Febbraio 2026
- 80% of Fortune 500 use active AI Agents: Observability, governance, and security shape the new frontier 10 Febbraio 2026
- Manipulating AI memory for profit: The rise of AI Recommendation Poisoning 10 Febbraio 2026
- [In preview] Public Preview: Application Gateway for Containers – AKS managed add-on 9 Febbraio 2026
- [In preview] Public Preview: Application Gateway for Containers – AKS managed add-on 9 Febbraio 2026
- A one-prompt attack that breaks LLM safety alignment 9 Febbraio 2026
- Analysis of active exploitation of SolarWinds Web Help Desk 7 Febbraio 2026
In today’s AI-first world, identity and network access are the first touchpoints for enforcing least privilege and protecting against sophisticated, identity-based attacks—but for many organizations, that defense is fragmented. Siloed teams and disconnected tools create security gaps, operational inefficiencies, and a poor user experience. The Microsoft Entra Suite[…]
Read More
In today’s fast-evolving landscape, where businesses balance on-premises systems and cloud resources, identity-based cyberthreats are growing more frequent and sophisticated. The question isn’t whether an identity attack will occur—but when. The numbers are staggering: In 2024 Microsoft saw an average of more than 7,000 password attacks happen per[…]
Read More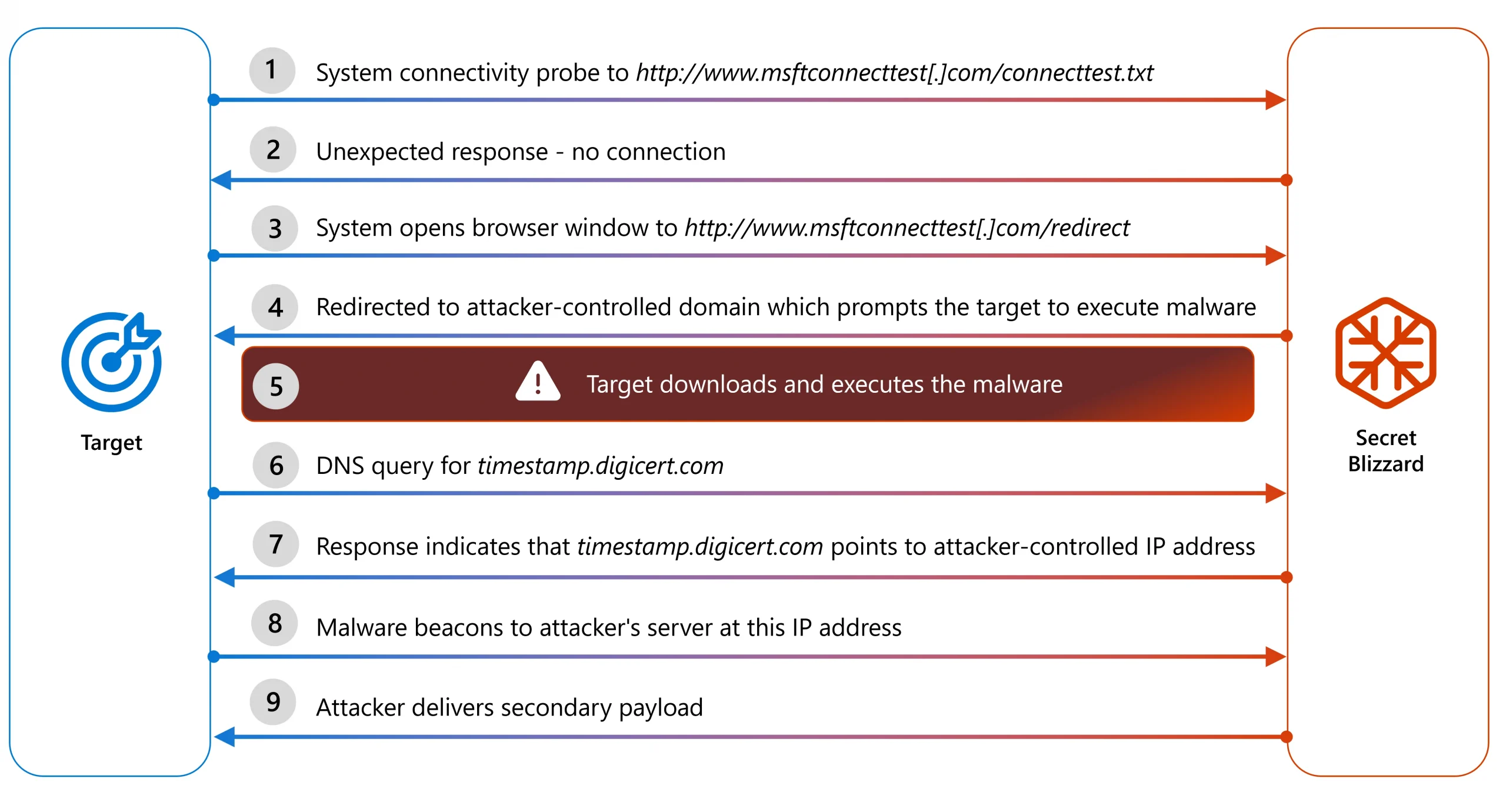
Microsoft Threat Intelligence has uncovered a cyberespionage campaign by the Russian state actor we track as Secret Blizzard that has been targeting embassies located in Moscow using an adversary-in-the-middle (AiTM) position to deploy their custom ApolloShadow malware. ApolloShadow has the capability to install a trusted root certificate to[…]
Read More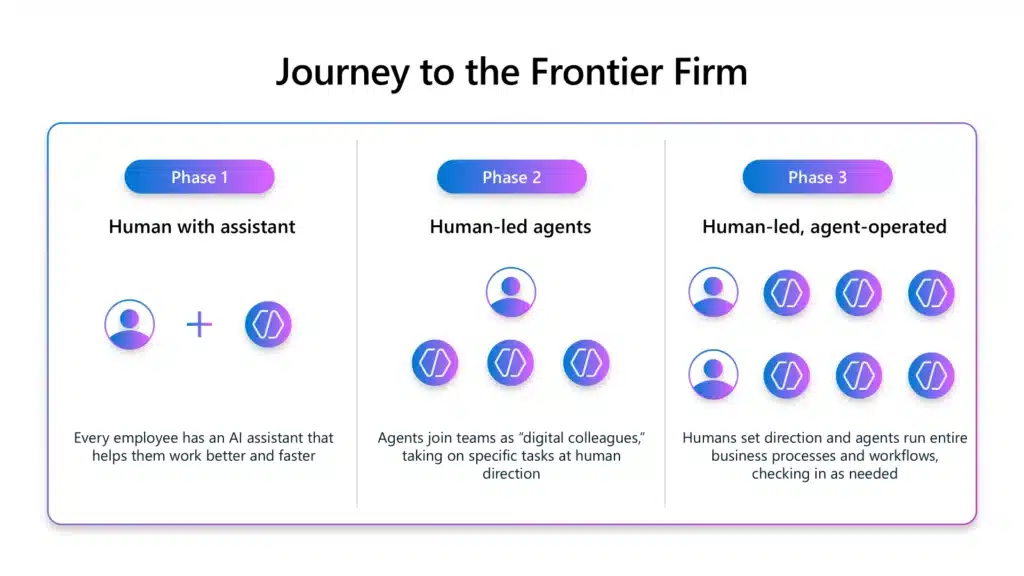
As AI agents evolve from on-demand assistants to autonomous agents, CIOs are entering a new era of governance. Traditional governance models designed for low-code apps and automation can be reused and evolved to meet increasing demands from more capable agents, with growing industry regulations. This expanded power brings[…]
Read More
We are excited to announce the return of the Power Platform Community Conference (PPCC), taking place in Las Vegas from October 28–30, 2025. Now in its fourth year, this conference is recognized by many in the community as the leading event for low-code enthusiasts, IT leaders, developers, and[…]
Read More
Securing websites can be daunting, especially if you don’t have a background in web security. From configuring headers to monitoring web traffic anomalies, staying on top of priorities can feel overwhelming. The Security Agent (public preview) in Power Pages simplifies this process by offering AI-driven recommendations, automated scans,[…]
Read More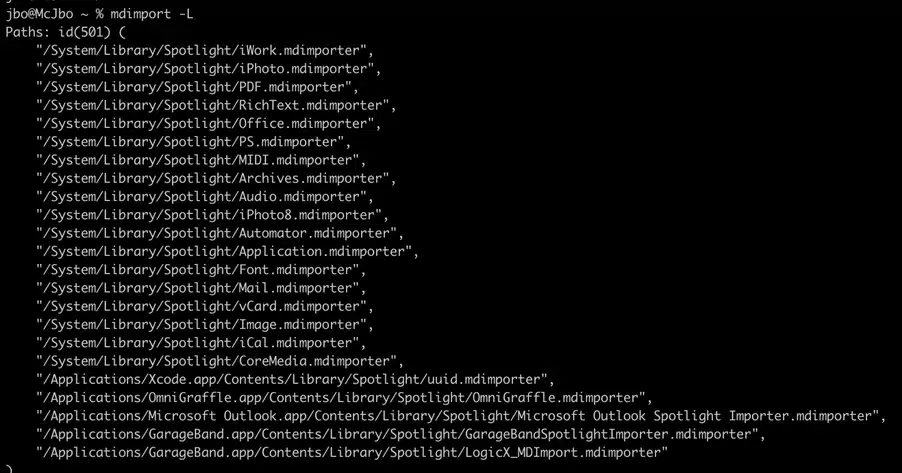
Microsoft Threat Intelligence has discovered a macOS vulnerability that could allow attackers to steal private data of files normally protected by Transparency, Consent, and Control (TCC), such as files in the Downloads folder, as well as caches utilized by Apple Intelligence. While similar to prior TCC bypasses like[…]
Read More
Microsoft Threat Intelligence has discovered a macOS vulnerability that could allow attackers to steal private data of files normally protected by Transparency, Consent, and Control (TCC), such as files in the Downloads folder, as well as caches utilized by Apple Intelligence. While similar to prior TCC bypasses like[…]
Read More
You can’t protect what you can’t see. Security operations teams have long been faced with the challenge of managing massive, fast-growing datasets, and the cost of scaling traditional data management tools to handle these data volumes has become unsustainable. We’re evolving our industry-leading Security Incidents and Event Management[…]
Read More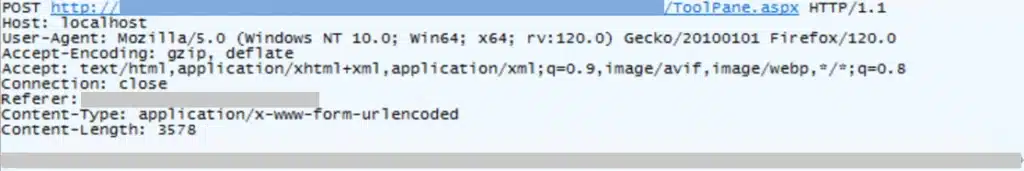
On July 19, 2025, Microsoft Security Response Center (MSRC) published a blog addressing active attacks against on-premises SharePoint servers that exploit CVE-2025-49706, a spoofing vulnerability, and CVE-2025-49704, a remote code execution vulnerability. These vulnerabilities affect on-premises SharePoint servers only and do not affect SharePoint Online in Microsoft 365.[…]
Read More