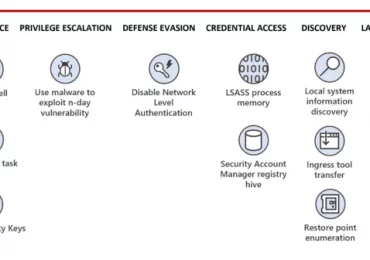
Summary Microsoft has identified a nation-state activity group tracked as Flax Typhoon, based in China, that is targeting dozens of[…]
Leggi di più
Each year, organizations face tens of billions of malware, phishing, and credential threats—with real-world impacts. When an attack succeeds, it[…]
Leggi di più
Microsoft’s cyberphysical system researchers recently identified multiple high-severity vulnerabilities in the CODESYS V3 software development kit (SDK), a software development[…]
Leggi di più
With more than 90 percent of organizations adopting a multicloud strategy1 and cloud-based cyberattacks growing 48 percent year over year,2[…]
Leggi di più
With more than 90 percent of organizations adopting a multicloud strategy1 and cloud-based cyberattacks growing 48 percent year over year,2[…]
Leggi di più
For the third consecutive year, Microsoft has been named a Leader in the Gartner® Magic Quadrant™ for Robotic Process Automation.[…]
Leggi di più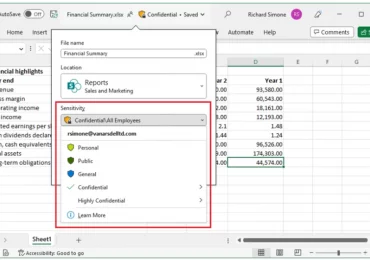
I recently worked with an enterprise customer who experienced a data exfiltration attack using the characteristics of the BazaCall campaign.[…]
Leggi di più
I recently worked with an enterprise customer who experienced a data exfiltration attack using the characteristics of the BazaCall campaign.[…]
Leggi di più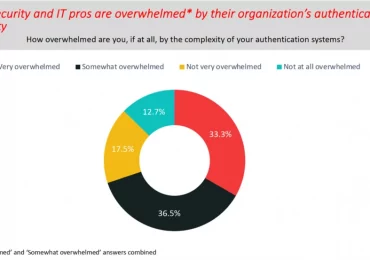
This blog post is part of the Microsoft Intelligent Security Association guest blog series. Learn more about MISA. Passwords are a security[…]
Leggi di più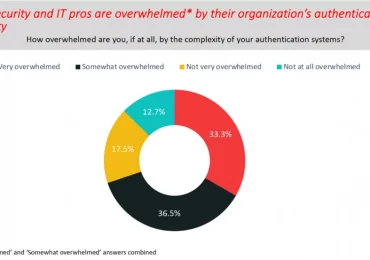
This blog post is part of the Microsoft Intelligent Security Association guest blog series. Learn more about MISA. Passwords are a security[…]
Leggi di piùThe recently published United States National Cybersecurity Strategy warns that many popular Internet of Things (IoT) devices are not sufficiently[…]
Leggi di più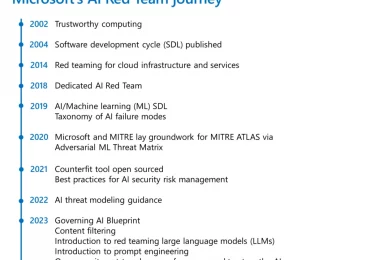
An essential part of shipping software securely is red teaming. It broadly refers to the practice of emulating real-world adversaries[…]
Leggi di più