Notizie per Categorie
Articoli Recenti
- [In preview] Public Preview: Azure Front Door Premium now supports Azure Private Link origins in UAE North 10 Febbraio 2026
- [In preview] Public Preview: Azure Front Door Premium now supports Azure Private Link origins in UAE North 10 Febbraio 2026
- [Launched] Generally Available: Azure Databricks Supervisor Agent 10 Febbraio 2026
- [Launched] Generally Available: Azure Databricks Supervisor Agent 10 Febbraio 2026
- 80% of Fortune 500 use active AI Agents: Observability, governance, and security shape the new frontier 10 Febbraio 2026
- Manipulating AI memory for profit: The rise of AI Recommendation Poisoning 10 Febbraio 2026
- [In preview] Public Preview: Application Gateway for Containers – AKS managed add-on 9 Febbraio 2026
- [In preview] Public Preview: Application Gateway for Containers – AKS managed add-on 9 Febbraio 2026
- A one-prompt attack that breaks LLM safety alignment 9 Febbraio 2026
- Analysis of active exploitation of SolarWinds Web Help Desk 7 Febbraio 2026

In the cybersecurity industry, there are many events to choose from. You as a cybersecurity professional are left wondering which events are worth your time. Each year, Microsoft hosts and participates in numerous events focused on equipping security professionals of all levels with the knowledge, skills, and tools[…]
Read More
The power of endpoint management Learn how to empower your workforce Today, we are taking a significant step in completing the delivery of functionality we promised when we first unveiled the vision for the Microsoft Intune Suite.1 We are launching three new solutions: Microsoft Intune Enterprise Application Management,[…]
Read More
Jupyter notebooks are continuing to grow in popularity in information security as an alternative or supplement to mainstream security operations center (SOC) tools. Notebooks can be used interactively for threat detection and response, or as automated tasks in a larger pipeline. Their flexibility and ability to combine code,[…]
Read MoreThe post Best practices in moving to cloud native endpoint management appeared first on Microsoft Security Blog. Source: Microsoft Security
Read MoreThe Microsoft security team detected a nation-state attack on our corporate systems on January 12, 2024, and immediately activated our response process to investigate, disrupt malicious activity, mitigate the attack, and deny the threat actor further access. The Microsoft Threat Intelligence investigation identified the threat actor as Midnight[…]
Read More
On January 25, 2024, we published the 2024 release wave 1 plans for Microsoft Dynamics 365 and Microsoft Power Platform, a compilation of new capabilities planned to be released between April 2024 and September 2024. This first release wave of the year offers hundreds of new features and improvements, showcasing our ongoing commitment[…]
Read More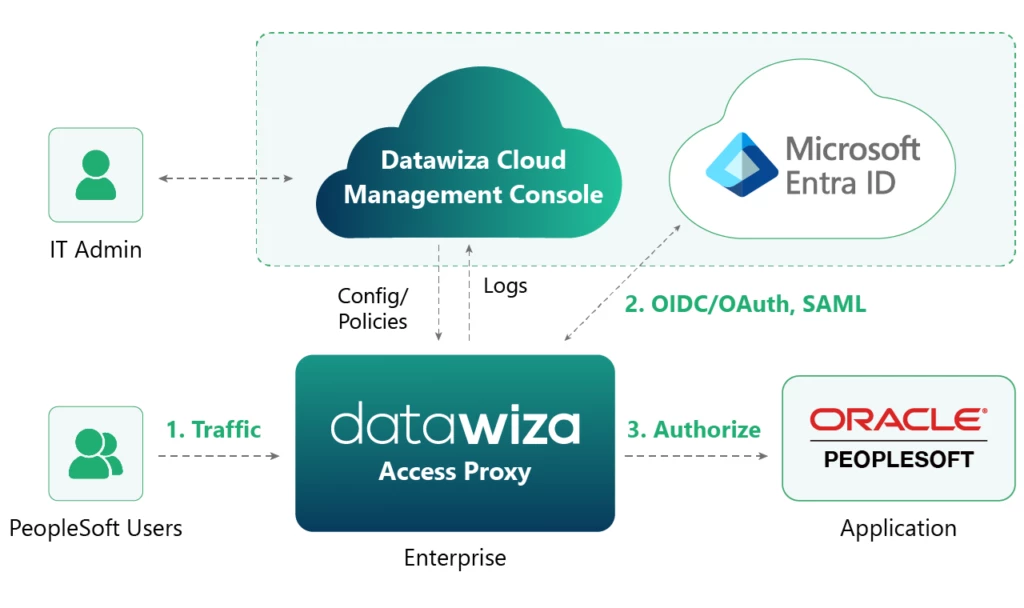
This blog post is part of the Microsoft Intelligent Security Association guest blog series. Learn more about MISA. In a scenario familiar to many universities worldwide, Claremont Graduate University (CGU), a renowned research university located in Southern California, was struggling with how to bring Oracle PeopleSoft Campus Solutions into its[…]
Read MoreThe legal profession is known for being cautious or hesitant to adopt new technologies. However, when it comes to AI, it seems like legal professionals are ready to be on the leading edge of AI implementation. A Thomson Reuters survey of legal professionals found that 82% agree that[…]
Read More
Today Microsoft Incident Response are proud to introduce two one-page guides to help security teams investigate suspicious activity in Microsoft 365 and Microsoft Entra. These guides contain the artifacts that Microsoft Incident Response hunts for and uses daily to provide our customers with evidence of Threat Actor activity[…]
Read More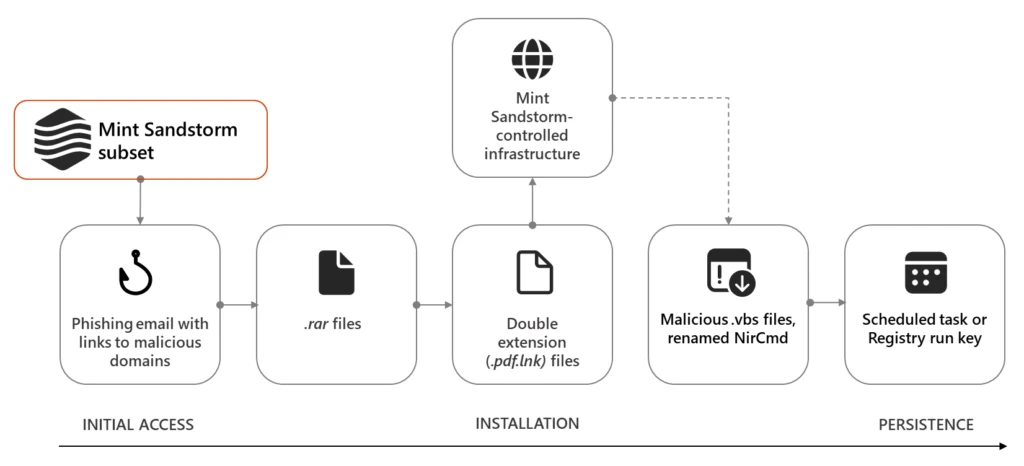
Since November 2023, Microsoft has observed a distinct subset of Mint Sandstorm (PHOSPHORUS) targeting high-profile individuals working on Middle Eastern affairs at universities and research organizations in Belgium, France, Gaza, Israel, the United Kingdom, and the United States. In this campaign, Mint Sandstorm used bespoke phishing lures in[…]
Read More