
Command-and-control (C2) servers are an essential part of ransomware, commodity, and nation-state attacks. They are used to control infected devices and perform malicious activities like downloading and launching payloads, controlling botnets, or commanding post-exploitation penetration frameworks to breach an organization as part of a ransomware attack. Blocking these[…]
Read More
Since 2014, United States criminal justice agencies have been managing Criminal Justice Information in Microsoft Azure Government. This cloud platform was developed to support critical compliance standards including the Federal Bureau of Investigation’s (FBI’s) Criminal Justice Information Services (CJIS) Security Policy and: Has the physical controls required by Section[…]
Read MoreCreate confidential VMs using Ephemeral OS disks for your stateless workloads. Source: Microsoft Azure – aggiornamenti
Read MoreAzure Maps Creator enables you to create Indoor Maps with GeoJSON. Source: Microsoft Azure – aggiornamenti
Read More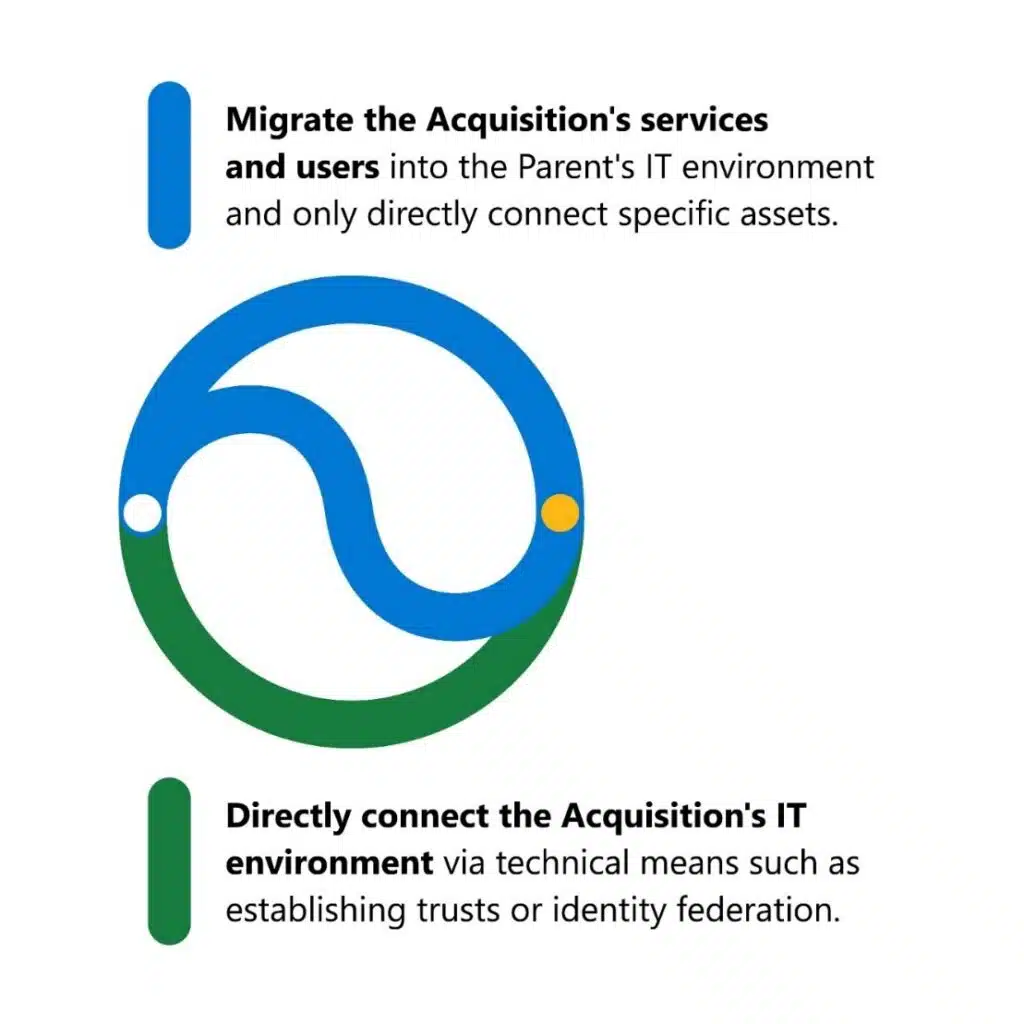
Sixty-two percent of organizations that undertake mergers and acquisitions face significant cybersecurity risks or consider cyber risks their biggest concern post-acquisition.1 Threat actors that focus on corporate espionage often target the acquiring company, which we will refer to as the Parent, early in the bidding process to gain[…]
Read MoreNotizie per Categorie
Articoli Recenti
- [In preview] Public Preview: Azure Front Door Premium now supports Azure Private Link origins in UAE North 10 Febbraio 2026
- [In preview] Public Preview: Azure Front Door Premium now supports Azure Private Link origins in UAE North 10 Febbraio 2026
- [Launched] Generally Available: Azure Databricks Supervisor Agent 10 Febbraio 2026
- [Launched] Generally Available: Azure Databricks Supervisor Agent 10 Febbraio 2026
- 80% of Fortune 500 use active AI Agents: Observability, governance, and security shape the new frontier 10 Febbraio 2026
- Manipulating AI memory for profit: The rise of AI Recommendation Poisoning 10 Febbraio 2026
- [In preview] Public Preview: Application Gateway for Containers – AKS managed add-on 9 Febbraio 2026
- [In preview] Public Preview: Application Gateway for Containers – AKS managed add-on 9 Febbraio 2026
- A one-prompt attack that breaks LLM safety alignment 9 Febbraio 2026
- Analysis of active exploitation of SolarWinds Web Help Desk 7 Febbraio 2026
