Customers can use configurable maintenance windows to schedule gateway maintenance for Point-to-Site VPN Gateway (P2S VPN) in Virtual WAN Service. With P2S VPN in Virtual WAN service now being generally available, customers can now configure maintenance w Source: Microsoft Azure – aggiornamenti
Read More
Microsoft Threat Intelligence has discovered a macOS vulnerability that could allow attackers to steal private data of files normally protected by Transparency, Consent, and Control (TCC), such as files in the Downloads folder, as well as caches utilized by Apple Intelligence. While similar to prior TCC bypasses like[…]
Read More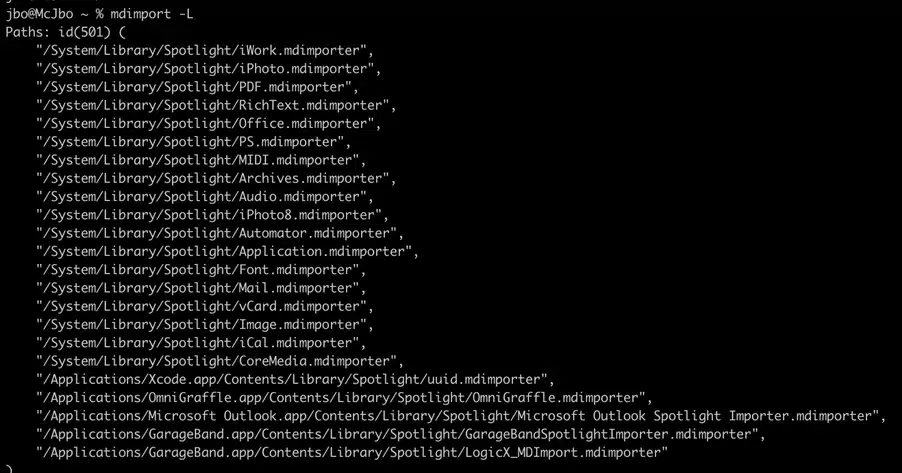
Microsoft Threat Intelligence has discovered a macOS vulnerability that could allow attackers to steal private data of files normally protected by Transparency, Consent, and Control (TCC), such as files in the Downloads folder, as well as caches utilized by Apple Intelligence. While similar to prior TCC bypasses like[…]
Read More
AI for grid operations: Key insights from our latest energy and resources webinar Electricity is no longer just a utility—it’s the backbone of modern life. From the devices in our homes to the data centers powering AI, demand for electricity is surging at a pace our current infrastructure[…]
Read More
AI for grid operations: Key insights from our latest energy and resources webinar Electricity is no longer just a utility—it’s the backbone of modern life. From the devices in our homes to the data centers powering AI, demand for electricity is surging at a pace our current infrastructure[…]
Read MoreNotizie per Categorie
Articoli Recenti
- [In preview] Public Preview: Azure Front Door Premium now supports Azure Private Link origins in UAE North 10 Febbraio 2026
- [In preview] Public Preview: Azure Front Door Premium now supports Azure Private Link origins in UAE North 10 Febbraio 2026
- [Launched] Generally Available: Azure Databricks Supervisor Agent 10 Febbraio 2026
- [Launched] Generally Available: Azure Databricks Supervisor Agent 10 Febbraio 2026
- 80% of Fortune 500 use active AI Agents: Observability, governance, and security shape the new frontier 10 Febbraio 2026
- Manipulating AI memory for profit: The rise of AI Recommendation Poisoning 10 Febbraio 2026
- [In preview] Public Preview: Application Gateway for Containers – AKS managed add-on 9 Febbraio 2026
- [In preview] Public Preview: Application Gateway for Containers – AKS managed add-on 9 Febbraio 2026
- A one-prompt attack that breaks LLM safety alignment 9 Febbraio 2026
- Analysis of active exploitation of SolarWinds Web Help Desk 7 Febbraio 2026
